The reality however, is totally different. I don't have cloud support
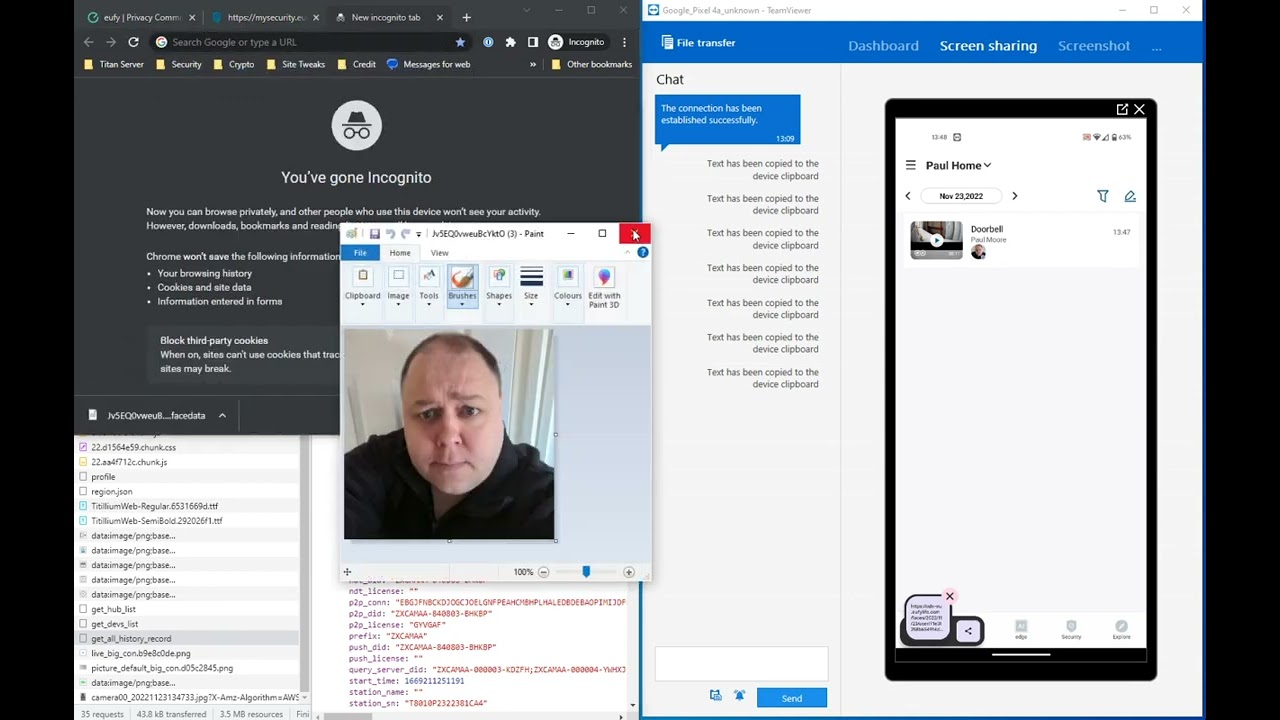
Paul Moore
I purchased a Eufy Doorbell Dual last week - believing it to be a private, locally-stored device. Eufy go to great lengths to convince you it's safe and accessible to you and only you.
The reality however, is totally different. I don't have cloud support
The reality however, is totally different. I don't have cloud support
updated 1 year ago
The reality however, is totally different. I don't have cloud support
This is also a lie.
They also claim that deleting the account complies with GDPR and automatically deletes all cloud-based footage. That too, is a lie.
DO NOT follow advice within this video. This is NOT OWASP grade content.
Fundamentals:
If you're trying to solve XSS on input, you don't understand the problem you're trying to solve. XSS is the process of escaping the current OUTPUT context and entering another. You can not safely sanitize inputs, as you've no way of knowing where that data will later be output; and that's the context that matters.
Validating inputs, sanitize outputs.
Clangers & Screw Ups:
12:59 - John (Director at Pervade, "joking" that he'd alter a pen test report so basic flaws like this wouldn't appear - many a true word....)
14:10 - Lacks basic understanding of IFRAMEs. Tries to load sites on the wrong protocol & sites which expressly prohibit framing with CSP (bbc, google etc).
30:00 - Jeez, literally clueless. Seems to think javascript won't execute after a page has loaded, so "no dynamic stuff".
31:00 - Seems to think this XSS attack is happening "server side" and because it is, we can now "insert code which does something"
31:24 - This isn't being "executed" by the server, what is he talking about?
32:03 - Genuinely believes a client-side language is being executed on the server. Is PHP node now?
33:25 - Just throw htmlspecialchars at everything - job done. Forget quotes, forget context - but at least he's doing it on output.
34:07 - Immediately renders the fix useless by running it against the inputs, not the output. This demonstrates a fundamental lack of understanding.
34:33 - Oh good lord, they're using the same technique for SQL injection mitigation!
34:54 - "We can now get more advanced" - Please do, this is cringe-worthy so far...
--- ADVANCED (BUT EQUALLY STUPID/INEFFECTIVE) STUFF ----
At this point, he moves away entirely from XSS mitigation and explains how to carry out basic input validation. This isn't necessary to protect against XSS.
35:15 - Using regex (preg_match) to find "the bad characters". Bad characters in what context? Again, missing the point entirely.
38:10 - "Sanitize our inputs so it can't do anything dangerous to us" - Sigh
38:32 - "We can also replace the bad characters" - This guy is the Director of Pervade, a "professional" company which provides apps for the Police, NHS etc. Think about that for a moment.
40:15 - Demonstrating a "stored XSS" attack - with fails aplenty.
47:00 - "You can do that on any page on the planet. There's actually no way for me to stop you doing that" (referring to inline XSS). Again, fundamental lack of understanding of basic security controls. A CSP (Content Security Policy) header is literally designed to protect against attacks like this, but it's the same CSP he couldn't figure out whilst trying to embed an IFRAME earlier.
48:55 - Genuinely seems to think he has to alter his code syntax to allow different inputs. HAHA
53:28 - Me asking him to demonstrate how to protect against XSS in his own code - he REMOVES THE BAD CHARACTERS! Writes software for Police/NHS remember!
56:13 - "To secure it, once again, it's one word - same as SQL injection" - Christ above. I give up.
1:05:30 - I ask him to explain how an application which requires characters which allow XSS, can protect against it. He goes on to explain nested ifs, database calls etc. An IF statement for every possible input - seems scalable!
1:09:50 - A glimmer of hope - "You can actually do this on the other side" - Referencing output encoding, which is actually how it should have been done an hour ago.
Please, don't run CyberAlarm on your network.
Suffice to say, it didn't go well. They not only ignored my request not to install any software (java, flash, adblock+, silverlight etc) but completely failed to fix Poodle.
This is the heavily shortened version. The full version (at 2hrs 10 minutes long) is here: youtube.com/watch?v=NwQojoLaxyA and is only edited to remove the phone number & postcode.
Suffice to say, it didn't go well. They not only ignored my request not to install any software (java, flash, adblock+, silverlight etc) but completely failed to fix Poodle.
This video features two calls to their "premium" technical support number, looking for more information on an exploit called "Poodle"; a flaw in SSL/TLS using CBC cipher suites.
Unsurprisingly, it didn't go entirely to plan.
With a 20 character, true random password consisting of mixalphanumerics & special chars and run through bCrypt (12 rounds), we're able to break it under 7 minutes.